This story was delivered to BI Intelligence “Payments Briefing” subscribers. To learn more and subscribe, please click here.
Concerns about data and information security remain a barrier to online shopping, according to new data from PayPal.
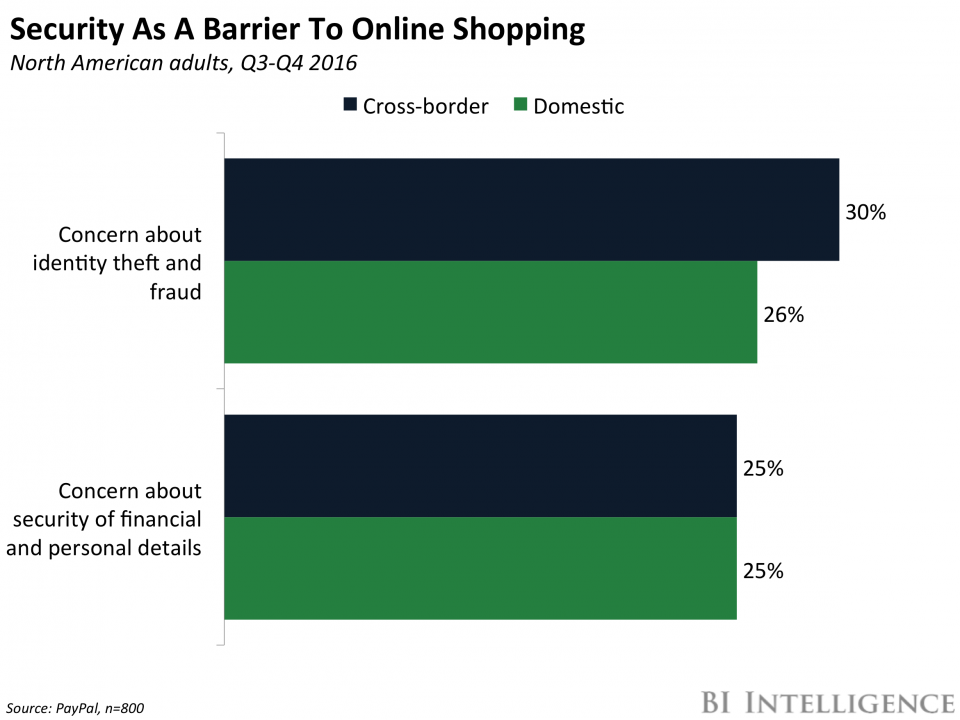
Among North American consumers, 25% of domestic and cross-border online shoppers saw concern about financial or personal data security as a barrier to shopping or shopping more often. Similarly, 26% and 30% respectively saw concern about identity theft and fraud as a barrier.
Those concerns aren’t unfounded.
- E-commerce fraud is rising rapidly. Both the number and average monthly value of fraudulent retail transactions rose in 2016, according to LexisNexis. But that’s especially prominent in digital channels — the cost per dollar of fraud grew 9-12% for online and mobile channels, compared to by just 3% for in-store purchasing.
- And it’s especially prominent in cross-border purchasing. Fraud in international channels is 2.5 times higher than domestic channels, according to LexisNexis.
But in order to continue growing their e-commerce volume, merchants and payment providers will need to work together to find a solution.
- Solving cross-border fraud is complicated. Merchants obviously want to ease consumer fears, or risk losing business. But fraud protection solutions, including increased manual review, often add layers and steps to the purchasing process, which could increase cart abandonment and decrease conversion rates. And they can also cause false declines, which are costly to merchants and can alienate consumers.
- But there are solutions that can be implemented to help ease fears without impacting the consumer experience too drastically. That means that there’s an opportunity in the market to provide solutions that can help ease some of these fears, and solve the problem without disrupting the consumer experience. Biometric authentication, like a fingerprint or iris scan, could be one such method, as could algorithm-based fraud solutions that analyze a purchase’s characteristics. It’s likely more merchants will invest in such services moving forward in order to make customers comfortable without making buying challenging.
Fraud cost U.S. retailers approximately $32 billion in 2014, up from $23 billion just one year earlier. To solve the card fraud problem across in-store, online, and mobile payments, payment companies and merchants are implementing new payment protocols that could finally help mitigate fraud.
John Heggestuen, senior research analyst for BI Intelligence, Business Insider’s premium research service, has compiled a detailed report on payment security that looks at how the dynamics of fraud are shifting across in-store and online channels and explains the top new types of security that are gaining traction across each of these channels, including on Apple Pay.
Here are some of the key takeaways from the report:
- EMV cards are being rolled out with an embedded microchip for added security. The microchip carries out real-time risk assessments on a person’s card purchase activity based on the card user’s profile. The chip also generates dynamic cryptograms when the card is inserted into a payment terminal. Because these cryptograms change with every purchase, it makes it difficult for fraudsters to make counterfeit cards that can be used for in-store transactions.
- To bolster security throughout the payments chain encryption of payments data is being widely implemented. Encryption degrades valuable data by using an algorithm to translate card numbers into new values. This makes it difficult for fraudsters to harvest the payments data for use in future transactions.
- Point-to-point encryption is the most tightly defined form of payments encryption. In this scheme, sensitive payment data is encrypted from the point of capture at the payments terminal all the way through to the gateway or acquirer. This makes it much more difficult for fraudsters to harvest usable data from transactions in stores and online.
- Tokenization increases the security of transactions made online and in stores. Tokenization schemes assign a random value to payment data, making it effectively impossible for hackers to access the sensitive data from the token itself. Tokens are often “multiuse,” meaning merchants don’t have to force consumers to re-enter their payment details. Apple Pay uses an emerging form of tokenization.
- 3D Secure is an imperfect answer to user authentication online. One difficulty in fighting online fraud is that it is hard to tell whether the person using card data is actually the cardholder. 3D Secure adds a level of user authentication by requiring the customer to enter a passcode or biometric data in addition to payment data to complete a transaction online. Merchants who implement 3D Secure risk higher shopping-cart abandonment.
In full, the report:
- Assesses the fraud cost to US retailers and how that fraud is expected to shift in coming years
- Provides 5 high-level explanations of the top payment security protocols
- Includes 7 infographics illustrating what the transaction flow looks like when each type of security is implemented.
- Analyzes the strengths and weakness of each payment security protocol and the reasons why particular protocols are being put in place at different types of merchants.
To get your copy of this invaluable guide, choose one of these options:
- Subscribe to an ALL-ACCESS Membership with BI Intelligence and gain immediate access to this report AND over 100 other expertly researched deep-dive reports, subscriptions to all of our daily newsletters, and much more. >> START A MEMBERSHIP
- Purchase the report and download it immediately from our research store. >> BUY THE REPORT
The choice is yours. But however you decide to acquire this report, you’ve given yourself a powerful advantage in your understanding of payments security.
 EXCLUSIVE FREE REPORT:
EXCLUSIVE FREE REPORT:5 Top Fintech Predictions by the BI Intelligence Research Team. Get the Report Now »